Our Solutions
Comprehensive Solutions.
Stronger Security.
We deliver end-to-end cybersecurity solutions that help organizations
protect their infrastructure, safeguard data, and stay resilient against
evolving threats.
How we Help
✔️ Understand your environment and risk exposure
✔️ Recommend suitable security technologies
✔️ Support deployment and integration
How we Help
✔️ Understand your environment and tisk exposure
✔️Support deployment and integration
Assist with optimication and ongoing guidance
✔️Understand your environment and risk exposure
Cybersecurity Challenges Are Evolving Rapidly
Cyber criminals today are better-equipped than ever. With the decreasing cost of computing power, widespread automation,
and easy sharing of tools and techniques, attacks have become-more frequent, sophiaticated, and withjuit to detect.
At the some time, modern IT.initiatives such as Cloud computing, SaaS adoption, BYOD, mobility, and software defined
networks (SDN) have signthrantly expanded organizational attack surfaces, and thesi.
As a result, organizations face inoreased exposure to advanced cyber threats targeting networks, endpoints, applications,
data, and cloud environments.
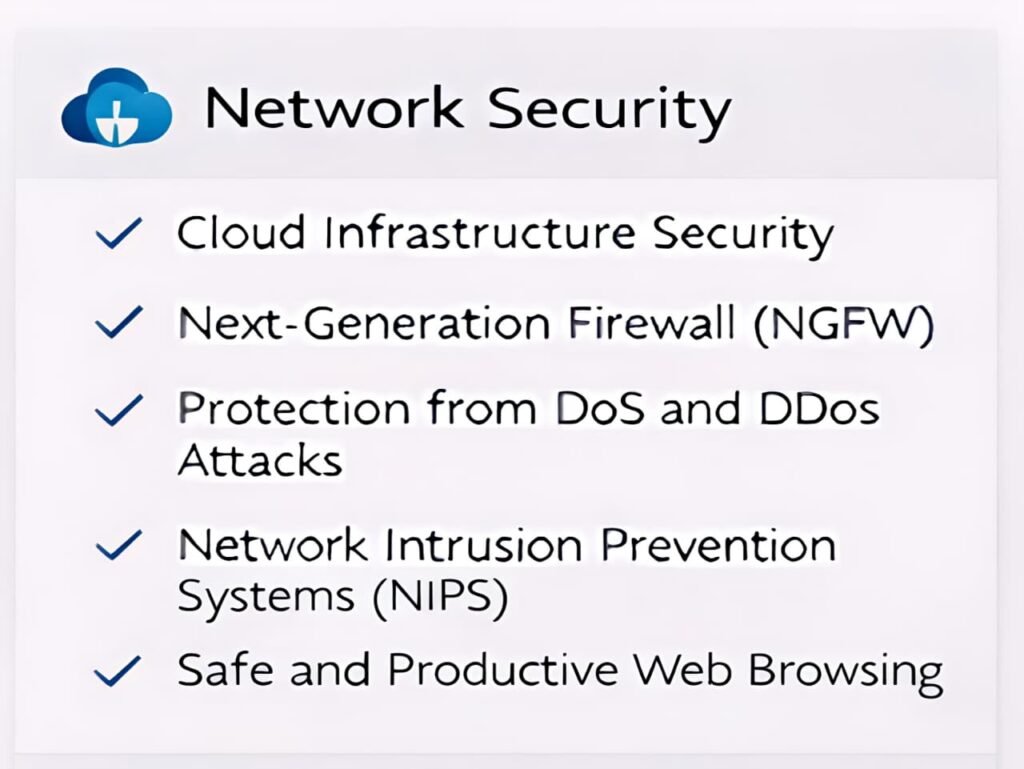
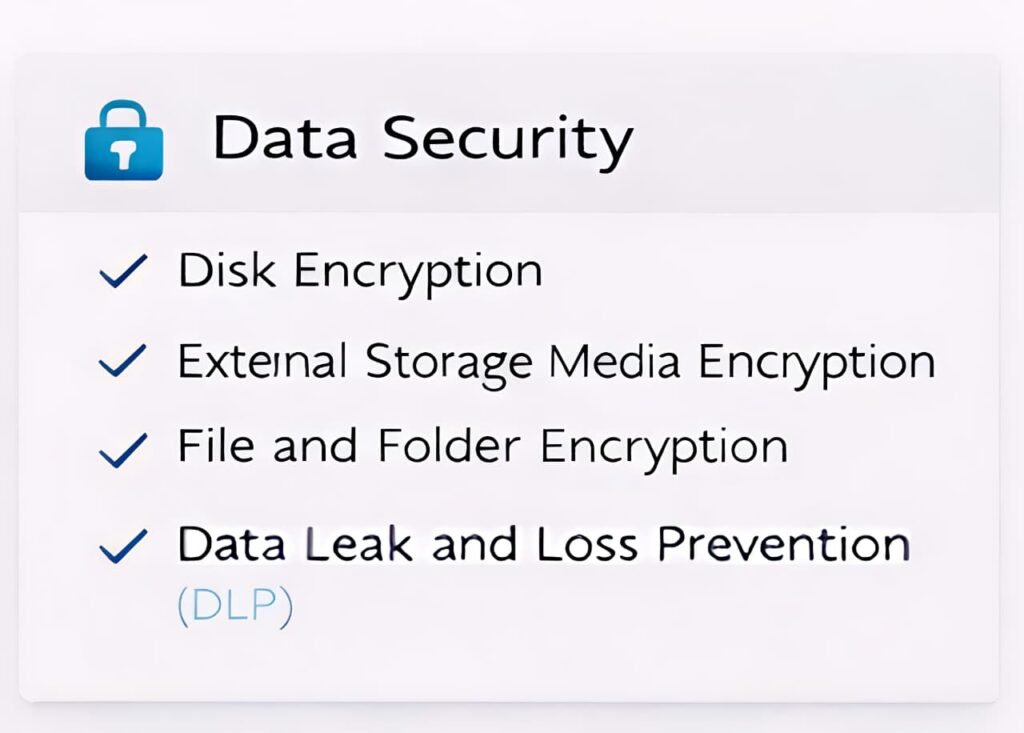
Our Cybersecurity Solution Portfolio
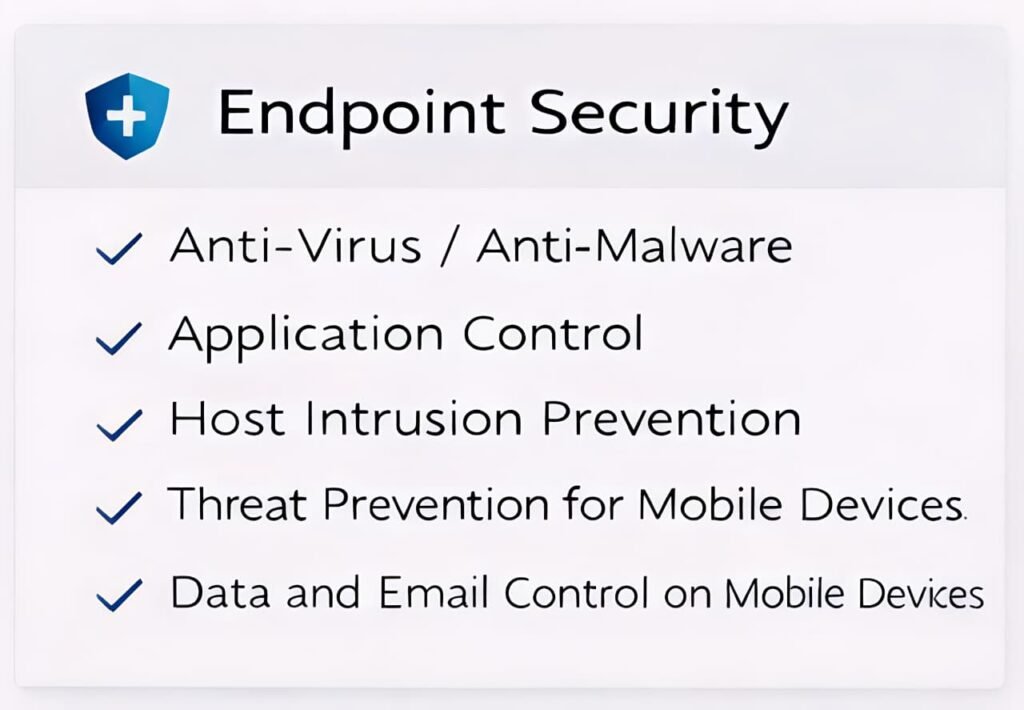



☑ Application Control
☑ Host Intrusion Prevention
☑ Threat Prevention for Mobile Devices
☑ Data and Email Control on Mobile Devices

☑ Next-Generation Firewall (NGFW)
☑Protection from DoS and DDoS Attacks
☑ Network Intrusion Prevention Systems (NIPS)
☑ Safe and Productive Web Browsing

☑ External Storage Media Encryption
☑ File and Folder Encryption
☑ Data Leak and Loss Prevention (DLP)

☑ Web Application Firewall (WAF)
☑ Load Balancer
☑ SSL Offload

☑ Cloud Workload Security
☑ Cloud Security Posture Management (CSPM)

☑ Anti-malware for Virtualized Servers and Desktops
☑ Protection for Data Storage Against Malware
☑ Security for Microsoft SharePoint

☑ Security Technology Recommendation
☑ Deployment & Integration Support

☑ Security Information & Event Management (SIEM)
☑ Network Access Control (NAC)
☑ Security Orchestration, Automation & Response (SOAR)
Our Approach

1. Assess
We asess your environment and understand your security challenges.

2. Recommend
We recommend the right solutions tallored to your requirements.

3. Implement
We deploy and integrate solutions with mimimal business disruption.

4. Optimize
We fine-tune and optimize for meximum performence and effectivenens.

5. Support
We provide continuous support and guidance for long=term success.

1. Assess
We asess your environment and understand your security challenges.

2. Recommend
We recommend the right solutions tallored to your requirements.

3. Implement
We deploy and integrate solutions with mimimal business disruption.

4. Optimize
We fine-tune and optimize for meximum performence and effectivenens.

5. Support
We provide continuous support and guidance for long=term success.
Tools & Technologies We Use


LET'S SECURE YOUR FUTURE
Ready to Strengthen Your Security Posture?
Our experts are here to help you build a secure, resilient,
and future-ready organiration.
