How we Help
✔️ Understand your environment and risk exposure
✔️ Recommend suitable security technologies
✔️ Support deployment and integration
How we Help
✔️ Understand your environment and tisk exposure
✔️Support deployment and integration
Assist with optimication and ongoing guidance
✔️Understand your environment and risk exposure
Our Cybersecurity Solution Portfolio
Looking for the Right Cybersecurity Solution?
Whether you are planning a new deployment or strengthening your existing security posture our team is ready to assist.
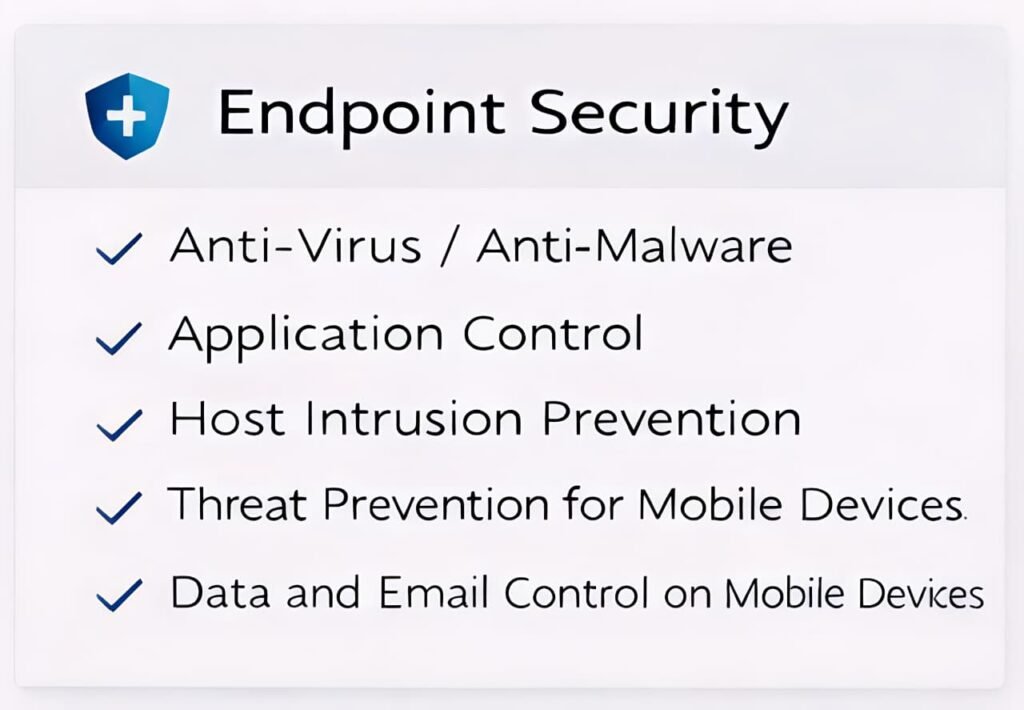



☑ Anti-Virus / Anti-Malware
☑ Application Control
☑ Host Intrusion Prevention
☑ Threat Prevention for Mobile Devices
☑ Data and Email Control on Mobile Devices
☑ Application Control
☑ Host Intrusion Prevention
☑ Threat Prevention for Mobile Devices
☑ Data and Email Control on Mobile Devices

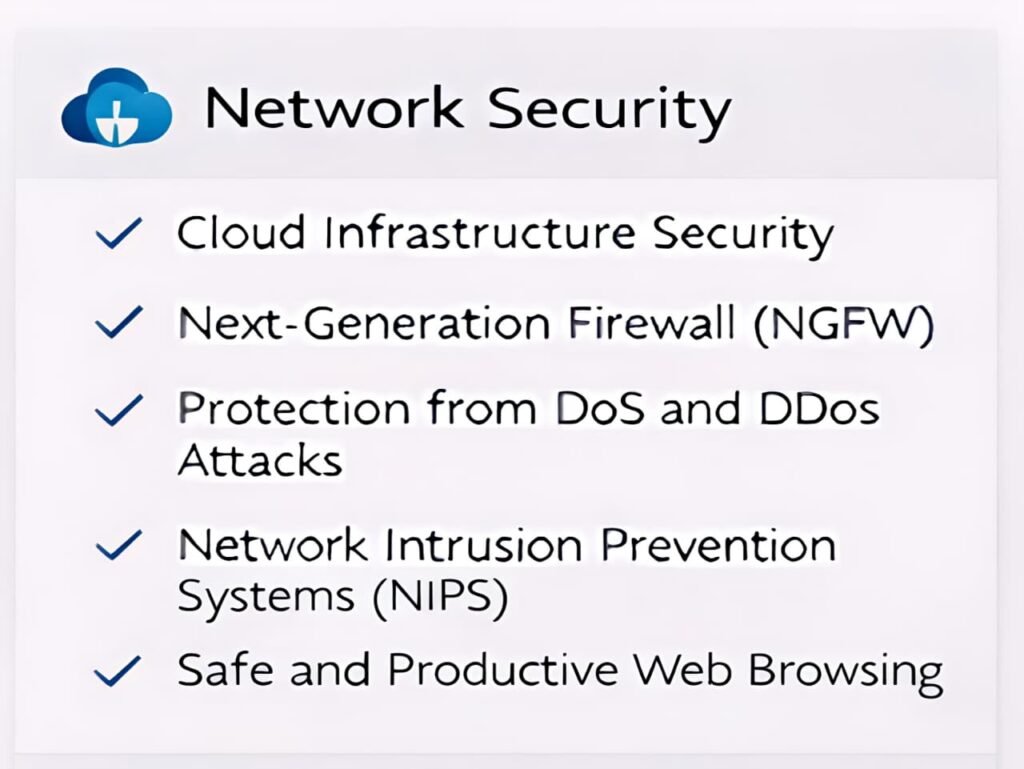
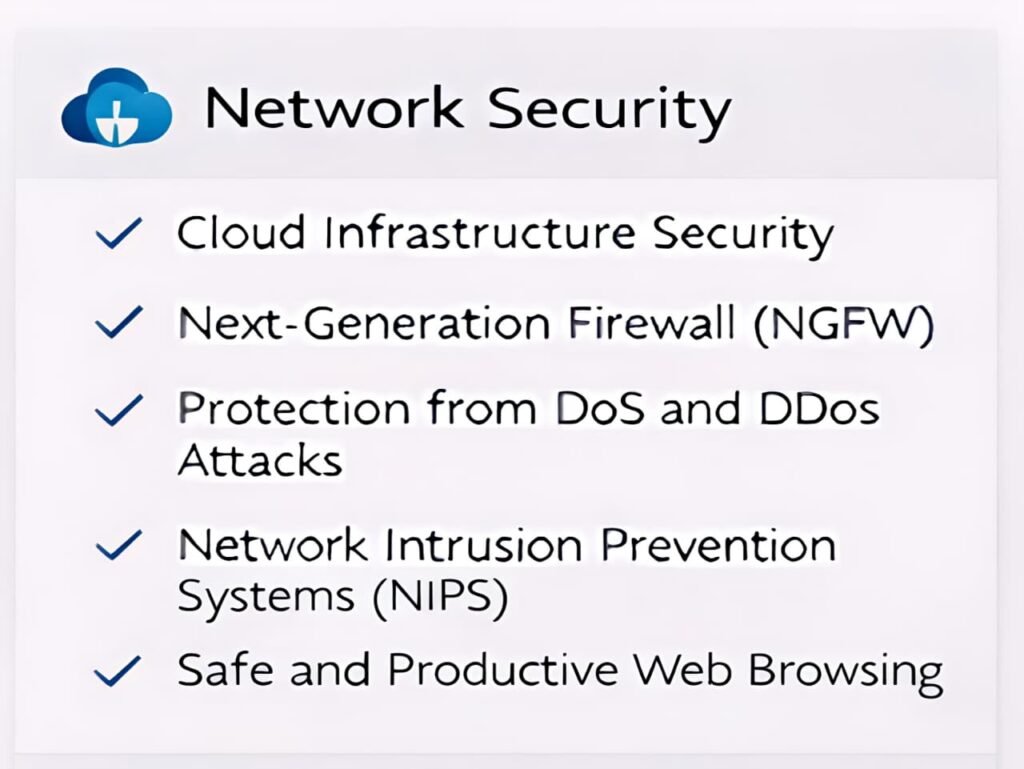
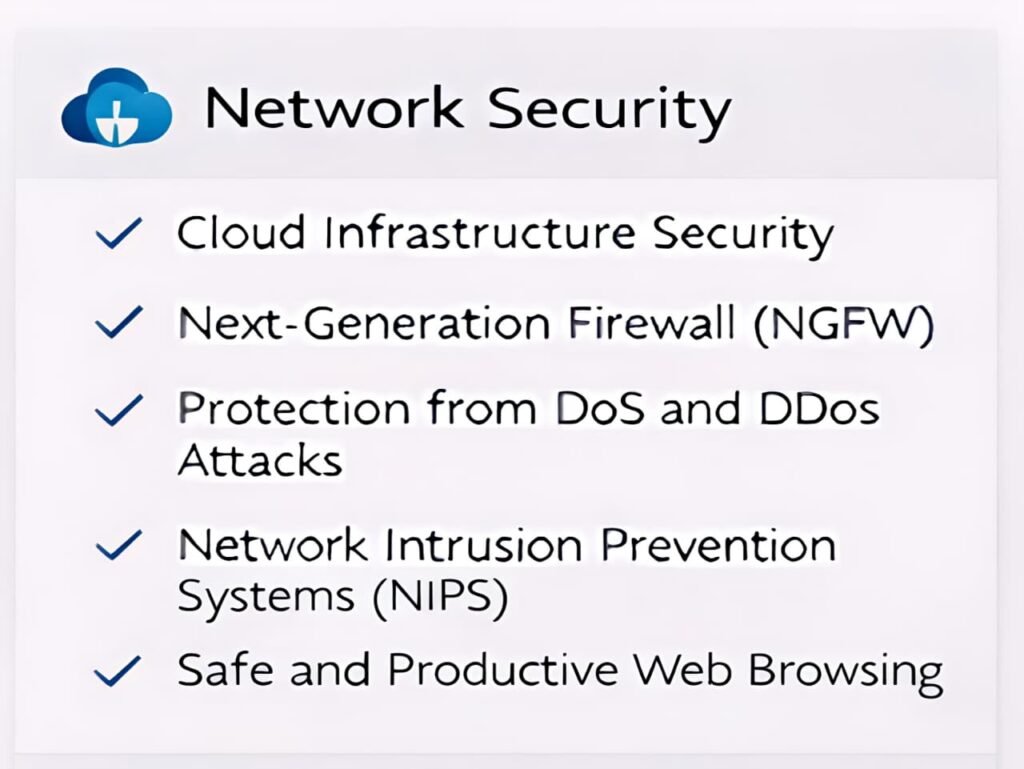
☑ Cloud Infrastructure Security
☑ Next-Generation Firewall (NGFW)
☑Protection from DoS and DDoS Attacks
☑ Network Intrusion Prevention Systems (NIPS)
☑ Safe and Productive Web Browsing
☑ Next-Generation Firewall (NGFW)
☑Protection from DoS and DDoS Attacks
☑ Network Intrusion Prevention Systems (NIPS)
☑ Safe and Productive Web Browsing

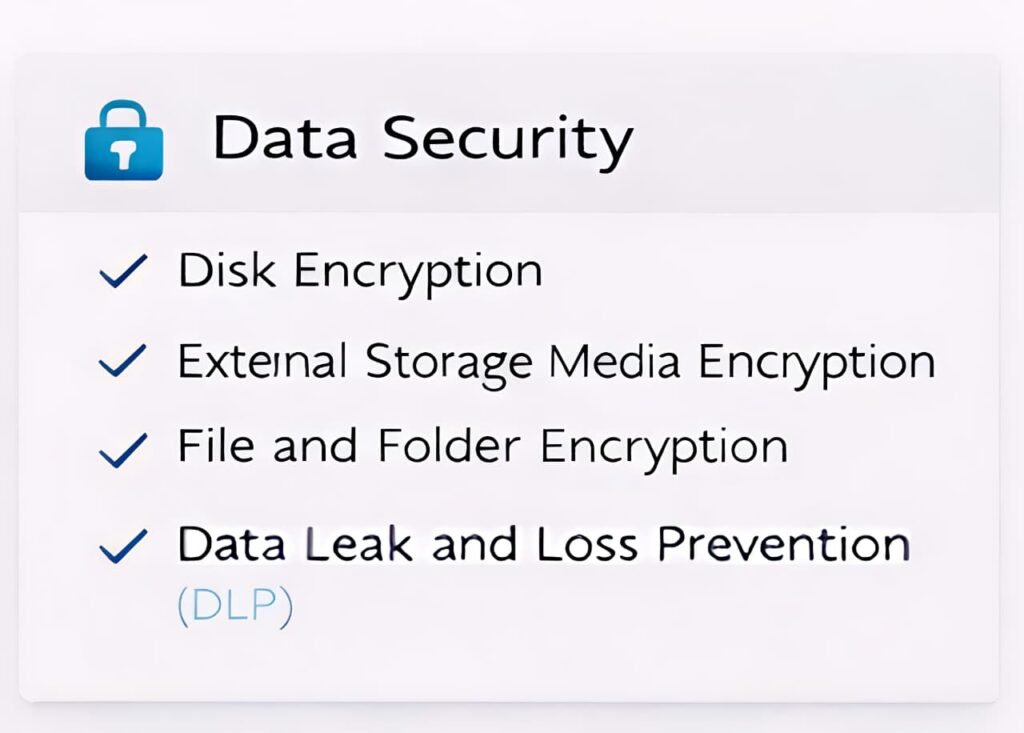
✔ Disk Encryption
✔ External Storage Media Encryption
✔ File and Folder Encryption
✔ Data Leak and Loss Prevention (DLP)
✔ External Storage Media Encryption
✔ File and Folder Encryption
✔ Data Leak and Loss Prevention (DLP)

☑ Authentication using Tokens or OTP
☑ Web Application Firewall (WAF)
☑ Load Balancer
☑ SSL Offload
☑ Web Application Firewall (WAF)
☑ Load Balancer
☑ SSL Offload

☑ Cloud Access Security Broker (CASB)
☑ Cloud Workload Security
☑ Cloud Security Posture Management (CSPM)
☑ Cloud Workload Security
☑ Cloud Security Posture Management (CSPM)

☑ Privileged Access Security
☑ Anti-malware for Virtualized Servers and Desktops
☑ Protection for Data Storage Against Malware
☑ Security for Microsoft SharePoint
☑ Anti-malware for Virtualized Servers and Desktops
☑ Protection for Data Storage Against Malware
☑ Security for Microsoft SharePoint

☑ Environment Assessment & Analysis
☑ Security Technology Recommendation
☑ Deployment & Integration Support
☑ Security Technology Recommendation
☑ Deployment & Integration Support

☑ Vulnerability Assessment
☑ Security Information & Event Management (SIEM)
☑ Network Access Control (NAC)
☑ Security Orchestration, Automation & Response (SOAR)
☑ Security Information & Event Management (SIEM)
☑ Network Access Control (NAC)
☑ Security Orchestration, Automation & Response (SOAR)
